2.6: The Value Chain
- Page ID
- 94870
\( \newcommand{\vecs}[1]{\overset { \scriptstyle \rightharpoonup} {\mathbf{#1}} } \)
\( \newcommand{\vecd}[1]{\overset{-\!-\!\rightharpoonup}{\vphantom{a}\smash {#1}}} \)
\( \newcommand{\dsum}{\displaystyle\sum\limits} \)
\( \newcommand{\dint}{\displaystyle\int\limits} \)
\( \newcommand{\dlim}{\displaystyle\lim\limits} \)
\( \newcommand{\id}{\mathrm{id}}\) \( \newcommand{\Span}{\mathrm{span}}\)
( \newcommand{\kernel}{\mathrm{null}\,}\) \( \newcommand{\range}{\mathrm{range}\,}\)
\( \newcommand{\RealPart}{\mathrm{Re}}\) \( \newcommand{\ImaginaryPart}{\mathrm{Im}}\)
\( \newcommand{\Argument}{\mathrm{Arg}}\) \( \newcommand{\norm}[1]{\| #1 \|}\)
\( \newcommand{\inner}[2]{\langle #1, #2 \rangle}\)
\( \newcommand{\Span}{\mathrm{span}}\)
\( \newcommand{\id}{\mathrm{id}}\)
\( \newcommand{\Span}{\mathrm{span}}\)
\( \newcommand{\kernel}{\mathrm{null}\,}\)
\( \newcommand{\range}{\mathrm{range}\,}\)
\( \newcommand{\RealPart}{\mathrm{Re}}\)
\( \newcommand{\ImaginaryPart}{\mathrm{Im}}\)
\( \newcommand{\Argument}{\mathrm{Arg}}\)
\( \newcommand{\norm}[1]{\| #1 \|}\)
\( \newcommand{\inner}[2]{\langle #1, #2 \rangle}\)
\( \newcommand{\Span}{\mathrm{span}}\) \( \newcommand{\AA}{\unicode[.8,0]{x212B}}\)
\( \newcommand{\vectorA}[1]{\vec{#1}} % arrow\)
\( \newcommand{\vectorAt}[1]{\vec{\text{#1}}} % arrow\)
\( \newcommand{\vectorB}[1]{\overset { \scriptstyle \rightharpoonup} {\mathbf{#1}} } \)
\( \newcommand{\vectorC}[1]{\textbf{#1}} \)
\( \newcommand{\vectorD}[1]{\overrightarrow{#1}} \)
\( \newcommand{\vectorDt}[1]{\overrightarrow{\text{#1}}} \)
\( \newcommand{\vectE}[1]{\overset{-\!-\!\rightharpoonup}{\vphantom{a}\smash{\mathbf {#1}}}} \)
\( \newcommand{\vecs}[1]{\overset { \scriptstyle \rightharpoonup} {\mathbf{#1}} } \)
\(\newcommand{\longvect}{\overrightarrow}\)
\( \newcommand{\vecd}[1]{\overset{-\!-\!\rightharpoonup}{\vphantom{a}\smash {#1}}} \)
\(\newcommand{\avec}{\mathbf a}\) \(\newcommand{\bvec}{\mathbf b}\) \(\newcommand{\cvec}{\mathbf c}\) \(\newcommand{\dvec}{\mathbf d}\) \(\newcommand{\dtil}{\widetilde{\mathbf d}}\) \(\newcommand{\evec}{\mathbf e}\) \(\newcommand{\fvec}{\mathbf f}\) \(\newcommand{\nvec}{\mathbf n}\) \(\newcommand{\pvec}{\mathbf p}\) \(\newcommand{\qvec}{\mathbf q}\) \(\newcommand{\svec}{\mathbf s}\) \(\newcommand{\tvec}{\mathbf t}\) \(\newcommand{\uvec}{\mathbf u}\) \(\newcommand{\vvec}{\mathbf v}\) \(\newcommand{\wvec}{\mathbf w}\) \(\newcommand{\xvec}{\mathbf x}\) \(\newcommand{\yvec}{\mathbf y}\) \(\newcommand{\zvec}{\mathbf z}\) \(\newcommand{\rvec}{\mathbf r}\) \(\newcommand{\mvec}{\mathbf m}\) \(\newcommand{\zerovec}{\mathbf 0}\) \(\newcommand{\onevec}{\mathbf 1}\) \(\newcommand{\real}{\mathbb R}\) \(\newcommand{\twovec}[2]{\left[\begin{array}{r}#1 \\ #2 \end{array}\right]}\) \(\newcommand{\ctwovec}[2]{\left[\begin{array}{c}#1 \\ #2 \end{array}\right]}\) \(\newcommand{\threevec}[3]{\left[\begin{array}{r}#1 \\ #2 \\ #3 \end{array}\right]}\) \(\newcommand{\cthreevec}[3]{\left[\begin{array}{c}#1 \\ #2 \\ #3 \end{array}\right]}\) \(\newcommand{\fourvec}[4]{\left[\begin{array}{r}#1 \\ #2 \\ #3 \\ #4 \end{array}\right]}\) \(\newcommand{\cfourvec}[4]{\left[\begin{array}{c}#1 \\ #2 \\ #3 \\ #4 \end{array}\right]}\) \(\newcommand{\fivevec}[5]{\left[\begin{array}{r}#1 \\ #2 \\ #3 \\ #4 \\ #5 \\ \end{array}\right]}\) \(\newcommand{\cfivevec}[5]{\left[\begin{array}{c}#1 \\ #2 \\ #3 \\ #4 \\ #5 \\ \end{array}\right]}\) \(\newcommand{\mattwo}[4]{\left[\begin{array}{rr}#1 \amp #2 \\ #3 \amp #4 \\ \end{array}\right]}\) \(\newcommand{\laspan}[1]{\text{Span}\{#1\}}\) \(\newcommand{\bcal}{\cal B}\) \(\newcommand{\ccal}{\cal C}\) \(\newcommand{\scal}{\cal S}\) \(\newcommand{\wcal}{\cal W}\) \(\newcommand{\ecal}{\cal E}\) \(\newcommand{\coords}[2]{\left\{#1\right\}_{#2}}\) \(\newcommand{\gray}[1]{\color{gray}{#1}}\) \(\newcommand{\lgray}[1]{\color{lightgray}{#1}}\) \(\newcommand{\rank}{\operatorname{rank}}\) \(\newcommand{\row}{\text{Row}}\) \(\newcommand{\col}{\text{Col}}\) \(\renewcommand{\row}{\text{Row}}\) \(\newcommand{\nul}{\text{Nul}}\) \(\newcommand{\var}{\text{Var}}\) \(\newcommand{\corr}{\text{corr}}\) \(\newcommand{\len}[1]{\left|#1\right|}\) \(\newcommand{\bbar}{\overline{\bvec}}\) \(\newcommand{\bhat}{\widehat{\bvec}}\) \(\newcommand{\bperp}{\bvec^\perp}\) \(\newcommand{\xhat}{\widehat{\xvec}}\) \(\newcommand{\vhat}{\widehat{\vvec}}\) \(\newcommand{\uhat}{\widehat{\uvec}}\) \(\newcommand{\what}{\widehat{\wvec}}\) \(\newcommand{\Sighat}{\widehat{\Sigma}}\) \(\newcommand{\lt}{<}\) \(\newcommand{\gt}{>}\) \(\newcommand{\amp}{&}\) \(\definecolor{fillinmathshade}{gray}{0.9}\)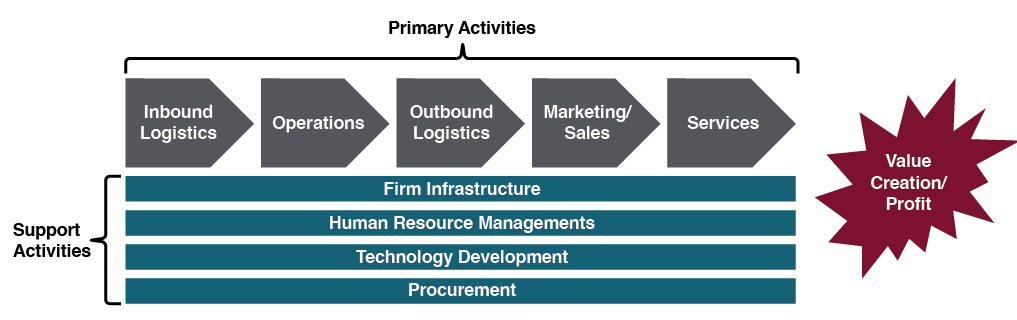
In his book Competitive Advantage: Creating and Sustaining Performance Michael Porter describes exactly how a company can create value and therefore profit. Value is built through the value chain, which is a series of activities undertaken by the company to produce a product or service. Each step in the value chain contributes to the overall value of a product or service. While the value chain may not be a perfect model for every type of company, it does provide a way to analyze just how a company is producing value. The value chain is made up of two sets of activities: primary activities and support activities. An explanation of these activities and a discussion of how information technology can play a role in creating value by contributing to cost advantage or differentiation advantage appears next.
Primary Activities
Primary activities are the functions that directly impact the creation of a product or service. The goal of a primary activity is to add value that is greater than the cost of that activity. The primary activities are:
- Inbound logistics. These are the processes that bring in raw materials and other needed inputs. Information technology can be used to make these processes more efficient, such as with supply-chain management systems which allow the suppliers to manage their own inventory.
- Operations. Any part of a business that converts the raw materials into a final product or service is a part of operations. From manufacturing to business process management (covered in Chapter 11), information technology can be used to provide more efficient processes and increase innovation through flows of information.
- Outbound logistics. These are the functions required to get the product out to the customer. As with inbound logistics, IT can be used here to improve processes, such as allowing for real-time inventory checks. IT can also be a delivery mechanism itself.
- Sales/Marketing. The functions that will entice buyers to purchase the products are part of sales and marketing. Information technology is used in almost all aspects of this activity. From online advertising to online surveys, IT can be used to innovate product design and reach customers as never before. The company website, or social media sites can serve as a sales channel itself.
- Service. Service activity involves the functions a business performs after the product has been purchased to maintain and enhance the product’s value. Service can be enhanced via technology as well, including support services through websites and knowledge bases.
Support Activities
The support activities are the functions in an organization that support all of the primary activities. Support activities can be considered indirect costs to the organization. The support activities are:
- Firm infrastructure. An organization’s infrastructure includes finance, accounting, enterprise systems (covered in Chapter 11) and quality control. All of these depend on information technology and represent functions where I.T. can have a positive impact.
- Human Resource Management. Human Resource Management (HRM) consists of recruiting, hiring, and other services needed to attract and retain employees. Using the Internet, HR departments can increase their reach when looking for candidates. I.T. also allows employees to use technology for a more flexible work environment.
- Technology development. Technology development provides innovation that supports primary activities. These advances are integrated across the firm to add value in a variety of departments. Information technology is the primary generator of value in this support activity.
- Procurement. Procurement focuses on the acquisition of raw materials used in the creation of products. Business-to-business e-commerce can be used to improve the acquisition of materials.
Imitation-resistant value chain
When a firm has an imitation-resistant value chain—one that’s tough for rivals to copy while gaining similar benefits—then a firm may have a critical competitive asset. From a strategic perspective, managers can use the value chain framework to consider a firm’s differences and distinctiveness compared to rivals. An analysis of a firm’s value chain can also reveal operational weaknesses, and technology is often of great benefit to improving the speed and quality of execution. Firms can often buy software to improve processes and tools (covered in Chapter 11) such as supply chain management (SCM; linking inbound and outbound logistics with operations), customer relationship management (CRM; supporting sales, marketing, and in some cases R&D), and enterprise resource planning software (ERP; software implemented in modules to automate the entire value chain). These tools can have a big impact on more efficiently integrating the activities within the firm, as well as with its suppliers and customers. While valuable, such software may not yield lasting competitive advantage if it can be easily matched by competitors as well.
If a firm adopts software that changes a unique process into a generic one, it may have co-opted a key source of competitive advantage particularly if other firms can purchase the same applications. This isn’t a problem with something like accounting software. Accounting processes are standardized and accounting isn’t a source of competitive advantage, so most firms buy rather than build their own accounting software. Using packaged, third-party SCM, CRM, and ERP software typically requires adopting a very specific way of doing things, using software and methods that can be purchased and adopted by others.
Enterprise Resource Planning Systems & Value Chain
During its period of PC-industry dominance, Dell stopped the deployment of the logistics and manufacturing modules of a packaged ERP implementation when it realized operational changes would be necessary. The changes required to implement the software modules would eliminate the firm’s unique supply chain advantages and would mean Dell would be effectively adopting the same practices as their competitors. By contrast, Apple had no problem adopting third-party ERP software because the firm competes on product uniqueness rather than operational differences.
This analysis of the value chain provides some insight into how information technology can lead to competitive advantage. Another important concept from Porter is the Five Forces Model, which is discussed in the next section.

