3.4: Using NIST SP.800-213A Capabilities for MIoT Security Assessment
- Page ID
- 85366
Using NIST guidance (augmented by federal law), FDA guidance and private-sector recommendations a simple framework can be created for assessing the level of cybersecurity and privacy protection a MIoT device possesses. By using the framework the level of overall compliance (with recommended standards) can be obtained which, in turn, can be used to determine acceptable levels of security and risk.
SP.800-213A, IoT Device Cybersecurity Guidance for the Federal Government: IoT Device Cybersecurity Requirement Catalog defines seven (7) distinct security Capabilities for IoT devices:
- Identification
- Configuration
- Protection
- Logical Access
- Software Update
- Cybersecurity State Awareness
- Device Security
In turn, each Capability contains one or more sub-Capabilities (e.g., Actions based on Device Identity). For each, sub-Capability there may be one or more Requirements (e.g., Ability to perform actions that can occur based on or using the identity of the device) which satisfy the sub-Capability. Finally, each Requirement may contain one or more sub-Requirements (e.g., Ability to hide IoT device identity from non-authorized entities) which satisfy the Requirement (Figure 1).
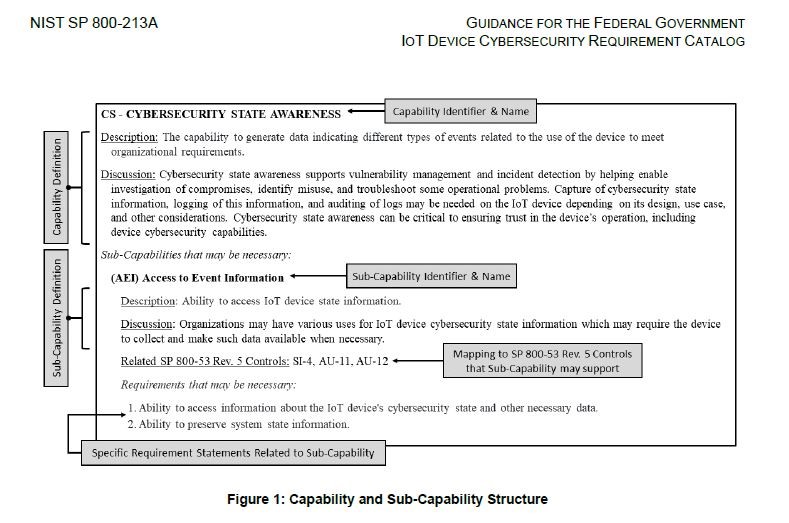
In addition, references to NIST Cybersecurity Framework and NIST.SP 800-53r5 (Security Control Catalog) are provided along with organizational Implications.
All told, SP.800-213A categorizes specific requirements as follows:
- 7 Capabilities
- 39 sub-Capabilities
- 257 Requirements & sub-Requirements
In terms of detail, Logical Awareness and Cybersecurity State Awareness Capabilities comprise 58% of the total requirements.
By assessing relative compliance with Requirements overall compliance can be assessed and quantified at the Capability & sub-Capability levels and further granulated at Requirement\sub-Requirement levels. This information can then be used to a) evaluate risk, b) identify MIoT weaknesses or vulnerabilities, c) gauge the level of IT management required and d) evaluate whether or not to allow the MIoT device into a network.


